Labview Vi Password Crack
They are so affordable now that people buy them for one event only and therefore cannot justify having to pack theirs up and carry it with them when they are tired and hungover. Clc genomics workbench download. When festival season begins, we see many of the main retailers advertise ‘festival packs’ that when spilt between a group, end up being the price of a few pints. Tents are becoming almost as single-use as plastics bottles.
.wow well that site is interesting. FYI it seems that the NI forum has found it as well.
For those of you that are interested the site appears to take a VI and overwrite the password with a known one, and then recalculate two hashes needed. It seems to me the person that owns that site must have some inside information from NI about the file structure. Not necessarily in how to parse the blocks of data (I can see that) but I'm not sure I would have been able to determine the two hashes that need to get recalculated when the password is changed. We've posted a Knowledge Base (KB) article on this subject;, which explains, in some detail, why the VI password protection feature is implemented as it is and the alternative available when stronger protection is required. We also plan to add a link to this KB in our product and/or help documentation, where appropriate, as part of our next major release. Our aim is to do our best to help users be aware of the issue and understand their options. I will monitor this thread for a bit and respond to questions or concerns as needed.
Sincerely, Roy Faltesek Senior Group Manager LabVIEW R&D National Instruments. What I was trying to say is hackers adapt every 6 months or so to crack the latest LabVIEW, which makes me think that the same effort could be put into cracking LabVIEW passwords.  The real problem lies in the fact that is doesn't even take a skilled cracker 6 months to adapt, but more like 6 hours or 6 days at worst. Using tools like Hey-Rays' IDA Pro you simply build a FLAIR recognition library that will help you seek out and identifies those hard-to-locate ASM functions in a matter of seconds. Once found, it's only a matter of setting some breakpoints, run the target in a debugger and locate the areas of interrest. Then go and do some NOP'ing Even the first time you have to disassemble an executable the size of the one for LabVIEW, there are some pretty good identifications tools out there that will sweep the file for any commonly known ASM routines. Like that of the MD5 hashing algorithm or the FlexLM/NET protection scheme functions.
The real problem lies in the fact that is doesn't even take a skilled cracker 6 months to adapt, but more like 6 hours or 6 days at worst. Using tools like Hey-Rays' IDA Pro you simply build a FLAIR recognition library that will help you seek out and identifies those hard-to-locate ASM functions in a matter of seconds. Once found, it's only a matter of setting some breakpoints, run the target in a debugger and locate the areas of interrest. Then go and do some NOP'ing Even the first time you have to disassemble an executable the size of the one for LabVIEW, there are some pretty good identifications tools out there that will sweep the file for any commonly known ASM routines. Like that of the MD5 hashing algorithm or the FlexLM/NET protection scheme functions.
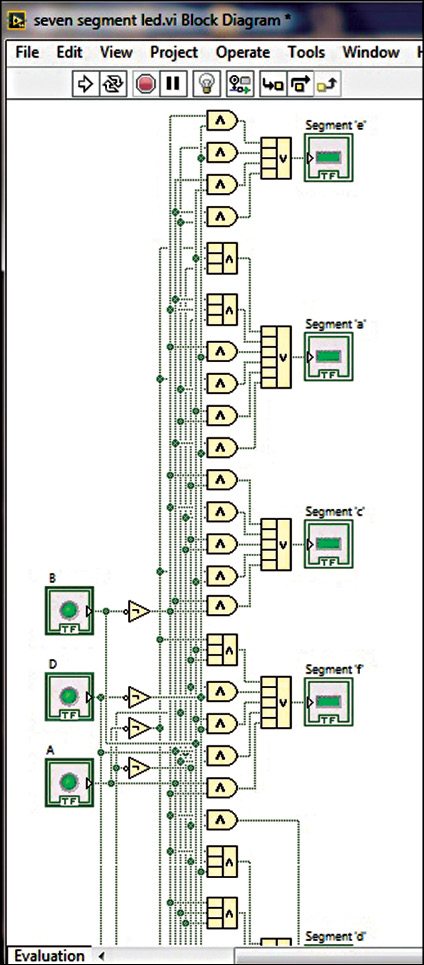
We gives you update version of NI LabVIEW Crack, you can download NI LabVIEW Crack 2017 for all version of windows, 10, 8 and 7. LabVIEW Serial Key: Furthermore, you can check latest invention in data communications, so, user can pass data between loops within single wire, and you do not have needed queues. Feb 1, 2018 - SolutionThere is currently no built-in way in LabVIEW to password protect VIs or deployed executables at run-time. It is possible to.
In either case constants like 0x123456789 or piecing strings together at runtime doesn't really make it harder to find these points of interrest. When talking about the VI security - As several people points out, the best protection really is to remove the block diagram and then put some trust into the fact that nobody has yet managed to Reverse Engineer the internal workings of the LabVIEW Runtime state machine. Or at least not that I know of. Correct me if i'm wrong here. I actually found a VI password cracker in Google's cache, and I tested it and it works. PM me if you want it. Sorry, no NI employees.